“How would you describe your work?’, I ask Elise. She does not need to think very long: ‘Puzzling for advanced users!’, she quickly replies. ‘I am basically trying to solve puzzles the whole day. Often more than one at the same time. The one puzzle is even more difficult than the other, but in the end, even the final piece fits.”
Elise and I are having coffee at a Covid-secure distance in a meeting room in the otherwise completely deserted office of Tesorion. Elise works here as an analyst at the Security Operations Centre, the SOC.
A day out of the life of a SOC analyst
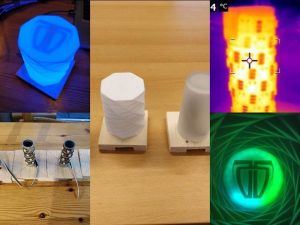
When I ask her about her average working day she answers: “If I have an early shift, then I am often the first to open the office. I start the inspection of the logs of the previous night with a cup of coffee. We installed sensors in the network of our customers with which we can monitor the infrastructure of the customer. We combine the data that they collect with “threat intelligence”. If deviations are observed, then tickets are generated automatically. On the basis of established rules, the monitoring system determines the “severity” of a ticket. An alarm sounds if it exceeds a certain value. At the SOC, this means that the border of the monitoring dashboard starts flashing in red. Due to the coronavirus measures, some of my colleagues are working from home. One of them has developed a lamp that the home-workers use next to their monitors. This lamp changes colour with the dashboard at the office.”
“Could you give me an example of an incident when the lamps coloured red?’, I ask. Elise smiles: ‘Many examples actually, but the work that I do is often highly confidential. We are familiar with the vulnerabilities of our customers. Information that is of considerable value to malicious parties. Moreover, our customers have their reputation to think about. But I can give you an anonymised example. Not too long ago, we noticed that on the network of one of our customers, unencrypted passwords were going through the network in a short period of time. Moreover, in a very short period of time, login had been tried for about twenty thousand times. We immediately contacted the customer. The customer took measures to stop the attack. In addition, we advised the customer how it can limit the chance of these kinds of attacks in the future. Besides, we often puzzle in pairs: that way we both contribute our personal qualities, and we keep each other sharp.”
Cooperation
When something does go wrong and the customer cannot fix it, we rely on our Computer Emergency Response Team (CERT). It will go on site and assist the customer in getting the incident under control, limiting the damages, and undoing potential consequences. For instance, in case of a ransomware attack.”
“When they are done, the CERT gives us feedback of their findings so that we can refine our monitoring tooling because, in addition to the puzzling, we also spend time on projects on a daily basis. Among other things to improve our automated interpretation of the monitoring data and to keep them up to date.”
“What do you like best about your work?’ ‘It is never boring’, says Elise. ‘Something can always happen; you must always be alert. The environment changes, the attack techniques change. Fortunately, I work in a tight team. There is ample mutual trust, we help each other, and we truly enjoy our work. It is allowed to make mistakes, and every once and a while we also have a good laugh, because we may be technicians, but we do have a sense of humour!”
“Is there also a disadvantage of the work that you do?’, I ask. Elise does not need to think long: ‘When I come home, I can never tell my partner what I have done at work…”
*This blog is the first of a series with which we provide readers a look behind the scenes of the SOC.